problem 1)a) prepare down four socket functions (C functions) used to create client/server applications.
b) prepare five layers in a typical TCP/IP computer network.
c) prepare down the services provided by TCP?
d) The source and destination port numbers are included in the packet header. Which layer needs to be able to read these port numbers?
problem 2)
a) If the FTP client is in active mode, what are the two FTP commands (protocol commands) issued by the client when the user issues:
ftp> ls
b) If the FTP client is in passive mode, what are the two FTP commands (protocol commands) issued by the client when the user issues:
ftp> get
c) How many concurrent connections does HTTP needs in order to download a single file? How many concurrent connections does FTP needs in order to download a single file?
d) Briefly describe what is a DNS (Domain Name Service) iterated query. Describe why this method is significant to keep the scalability of the DNS.
problem 3)
a) A distributed system uses UDP to transfer files between nodes. You are asked to design a simple reliable protocol to replace it. What are the necessary elements which you need to include in such a protocol? Your solution must focus on possible lost and damaged packets, not performance.
b) Describe the difference between Go-Back-N and Selective Repeat. Given a choice, which one is better for the performance of the network?
c) Describe the difference between “Congestion Control” and “Flow Control” from the view point of a transport protocol.
problem 4)
a) prepare down the two significant functions provided by the network layer protocols? Emphasize the importance of the difference between the two functions.
b) The network administrator checks an Ethernet card configuration using the command ipconfig. He extracts the values for the IP address and for the Mask:
IP address 192.123.246.12
Mask 255.255.255.128
prepare two exs of IP addresses that this machine can access:
1) one IP address that is accessible directly (no routing) by this machine.
2) one IP address that is only accessible via the gateway (router).
c)
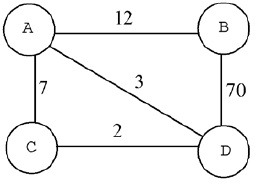
There are four routers connected via certain links in above figure. Assume that the following table is used for the initialisation of D’s routing table:
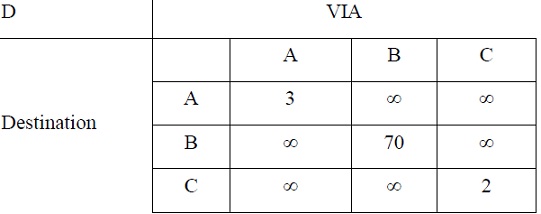
And the minimum cost is an array of 4 integers in the order A, B, C, D:
A advertises its minimum costs as: 0, 12, 7, 3
B advertises its minimum costs as: 12, 0, ∞, 70
C advertises its minimum costs as: 7, ∞, 0, 2
Demonstrate the first update on D’s table if node D simultaneously receives packets with the minimum cost information from the routers A, B and D.
d) There are possibly hundreds of millions of IP addresses in the Internet. Describe why the routing tables in TCP/IP routers do not need to contain lots of entries, and are usually rather small.
problem 5)
a) What is the purpose of CRC (Cyclic Redundancy Check)?
b) find out the CRC value for the character “1110 0001” considering:
i) the algorithm uses a standard polynomial method with 16 bits
ii) the generator is 0x8005
iii) no reverse bytes, no reverse results
prepare the final result of the CRC in hexadecimal.
c) Collisions are a challenging problem for data link protocols. Describe the main differences between data-link layer protocols for wired networks and protocols for wireless networks.
d) Describe briefly how the ARP protocol keeps table with the IP addresses and correspondent MAC (hardware) addresses.