The assignment is designed to help you develop skills and strengthen your understanding of data communications. Answer the questions as if they are a professional presentation to a client. Thus justify what you say in terms of what will work well for the client. Your submission should be around 5 to 10 pages, but be succinct.
Question 1: Network Stack
The essential qualities of any system are correctness, reliability, robustness and security, compatibility and scalability, ease of use, and efficiency. Consider for each of these how the physical, data-link, and Internet layers contribute to these qualities and how the higher layers add these qualities to the lower layers. You should submit around 3/4 to one page for each layer, but as always your answers should be well structured and to the point.
Question 2: A Day in the Life
You are an Internet messenger (a somewhat fictional entity, but it will make for an interesting story) who carries messages around the network. In the network below, a user turns on Computer A, starts a web browser, enters a URL to his favourite web site http://www.widgetsrus.com. The web browser asks you, the messenger, to carry a request to the web server and then carry a response back to the user. Your journey will take you into the caverns of the Internet as shown in the diagram below carrying the user’s request. The server – at Computer B – warmly receives you and formulates a reply to the request which you transport back to the user at Computer A.
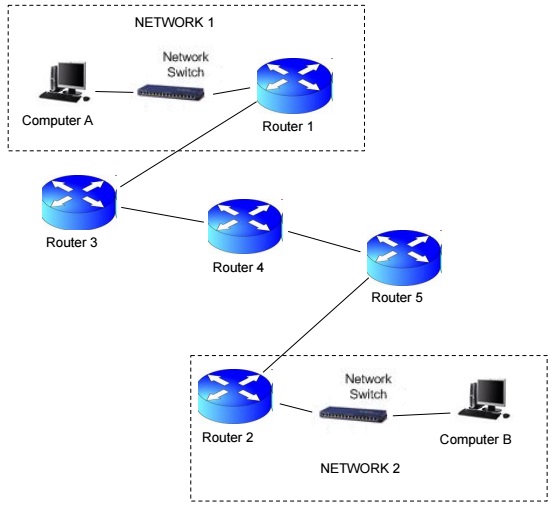
You should consider what happens at Computer A in the web browser, what happens to the message down through the stack layers, what happens to the message as it is sent across a wired Ethernet link. What does the switch do and which network layers are involved. What do the routers do and which layers are involved at the routers. How do the switches and routers process (manipulate) the packets? What fields do they look at, and which fields are changed? You only need to report in detail your experience at router 1 and router 2 – it will be much the same for routers 3, 4, and 5.
What happens to the message you are carrying at the web server on Computer B? How is the reply constructed and do you return it to the user in the reverse process. Where information is the same as in the outward journey, you need not repeat it.
We have not done everything in detail in the lectures yet, but you should aim to get a feeling for how all messages are processed in the network, and the slightly different terminology used at each stack layer. This will help you to place the detail we give in lectures and what the fields in the packet headers are used for.
You can write this as a story – but it must be a very interesting story. Better still would be presentation in tabular form so that the reader can see what you have found out at a glance. You should present the encapsulation and decapsulation of the messages at each node that the message passes through.
This answer will most likely take 3 to 4 pages.
Question 3: IP Addressing
a) Perform the following boolean operations on the given bit patterns
i. not 0010111000101100
ii. 0010111000101100 or 1110000011100001
iii. 0010111000101100 and 1110000011100001
b) What are the subnet masks for the following slash address blocks?
i. /8
ii. /15
iii. /29
c) Are the following address masks legal? If so, what are their slash forms? If not, why are they not legal? rks)
i. 255.255.248.0
ii. 255.224.252.0
iii. 255.255.255.224
iv. 255.255.156.0
d) How many computers are in networks with the following address blocks?
i. /13
ii. /26