Task 1: Review Questions
Anwers the following questions on a separate sheet during lectue and submit. Students should perform this task individually.
1. List three approaches to message authentication.
2. What is a message authentication code?
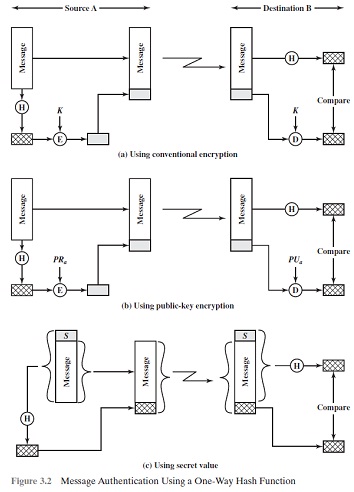
3. Briefly describe the three schemes illustrated in Figure 3.2.
4. What properties must a hash function have to be useful for message authentication?
5. In the context of a hash function, what is a compression function?
6. What are the principal ingredients of a public-key cryptosystem?
7. List and briefly define three uses of a public-key cryptosystem.
8. What is the difference between a private key and a secret key?
9. What is a digital signature?
Task 2: Problems
Anwers the following questions on a separate sheet during lectue and submit.
Students should perform the steps in this task individually.
1. State the value of the padding field in SHA-512 if the length of the message is
a) 1919 bits
b) 1920 bits
c) 1921 bits
2. 3.4 State the value of the length field in SHA-512 if the length of the message is
a) 1919 bits
b) 1920 bits
c) 1921 bits
3. Show the result of encrypting M = 4 using the public key (e; n) = (3; 77) in the RSA cryptosystem.
4. What is the plaintext for the following ciphertext, which was encrypted using a simple substitution cipher: CJBT COZ NPON ZJV FTTK TWRTUYTFGT NJ DTN O XJL. Y COZ ZJV CPJVIK DTN O XJL MYUCN.
Full Alphabet mapping: O = A, L = B, G = C, K = D, T = E, M = F, D = G, P =H, Y = I, X = J, E = K, I = L, B = M, F = N, J = O, R = P, H = Q, U = R, C = S, N= T, V = U, S = V, Q = W, W = X, Z = Y, A = Z.