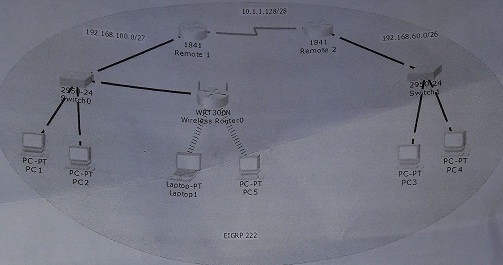
Refer to the exhibit, Central HQ recently installed a new router in their Remote 1 and Remote 2. Complete the network installation by performing the initial router configurations and configuring EIGRP routing using the router command line interface (CLI) on Remote 1 and
Remote 2.
1. Configure both routers per the following requirements :
- Name of the router is Remote 1 and Remote 2.
- Enable -secret password is cisco
- The password to access user EXEC mode using the console is ciscol
- The password to allow telnet access to the router is cisco2
- Interfaces should be enables. Routing protocol is EIGRP. Configure host using the given IP address.
- Configure Wireless Router to enable Laptop1 and PC5 can communicate via network.
2. The successful of this configuration is when all Host successful ping each.
3. Please note that management has decided that this HOST PC1 should not connect to HOST PC4.
Save your file using your registration number.
Write your all configuration command & submit to your lecturer.
Submit softcopy & hardcopy to your lecturer.