Title: Perimeter Network Security System
Outline Requirements:
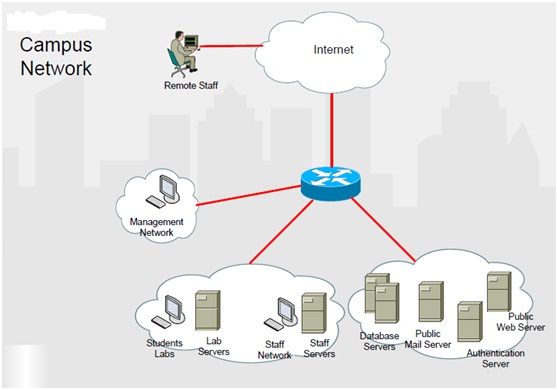
The University is based in Glasgow, and offers higher education services to its students and staff. It is situated on a single campus called Campus A. Students and staff employs the network services from hosts on various different user networks, as shown in figure below:
Due to a raising number of security violations, a possible redesign of the network infrastructure is to be investigated. You have been hired as a consultant to offer security enhancements, and produce a report. The main aim of the exercise is to present a possible solution to the problem at hand by making a prototype of the new network security infrastructure. This new design must tackle the given components:
• Offer best practice network egress and ingress filtering at the network perimeter.
• Make a perimeter firewall, with a suitable topology to give the organizations services, comprising public web and mail servers. The firewall must have a closed security stance, and provide public services in a secure manner.
• Offer secure access to all devices, from the security management subnet.
In addition, research must be carried out into increasingly common Advanced Persistent Threats (APT), and ways to defend against such using network defenses. This section of the coursework will be research only and be confined to a part of the Research Section.
You will be needed to analyze the new system needs and design, implement and justify a prototype for each and every component of the proposed system. Your proposed system can be implemented on Cisco hardware deployed in the network lab, or on the virtual networking software (like GNS3). The system must clearly demonstrate your mastery of the course material. Each and every component of the system must be developed separately, and it is not essential to implement an entire working system.
Introduction:
describe an understanding of the problem specification, the challenges and research, design and implementation.
Research and Design:
This must exhibit an outline of the proposed system and the main design features.
• Offer short literature review for each of the proposed key components (describeing research from a variety of sources, critical evaluation and personal reflection).
• Provide design of network security system components and justify your decisions.
Prototype Implementation:
This must define an outline prototype implementation of the system.
• Implement the key components of the proposed network system design (describes and show illustrations of your implementation comprising diagrams as there will not be practical demonstration).
Testing and Evaluation:
This must show testing, and outline the outcomes of any evaluations that you have made.
• describe and demonstrate the testing methods used, and show the outcome of the testing.
• Include evaluation of the systems and technologies used, by using references to the literature and personal reflection.
Conclusions:
This must reflect the methods you have used in the report, and to assess their benefits and limitations, and any observations that you have gained.
• Draw conclusions regarding the network security systems created, comprising conclusions regarding your design and also the implementation.
• Any recommended future enhancements, based on your findings.
References/Presentation:
Full academic referencing of books, web sites, and papers, by using thorough APA/Harvard referencing format.
• All references should be defined in an APA/Harvard format, and must be listed at the end of the report.
• Reference all materials employed, and cite every reference in the body of the report.
• Total report size must be 15-20 pages that do not comprise cover page, and appendix - if any.
• The report must be in 11 point text with normal margins.
• The similarity must be below 7%. Numbers above 7% indicate a possible problem.