Assignment
1. Consider a TCP connection between Host A and Host B. Suppose that the TCP segments traveling from Host A to Host B have source port number 12048 and destination port number 80. What are the source and destination port numbers for segments traveling from Host B to Host A?
2. Suppose a process in Host C has a UDP socket with port number 6789, Suppose both Host A and Host B each send a UDP segment to Host C with destination port number 6789. Will both of these segments be directed to the same socket at Host C? If so, how will the process at Host C know that these two segments originated from two different hosts?
3. Suppose that a Web server runs in Host C on port 80. Suppose this Web server uses persistent connections, and is currently receiving requests from two different Hosts, A and B. Are all of the requests being sent through the same socket at Host C? If they are being passing through different sockets, do both of the sockets have port 80? Discuss and explain.
4. True or false? Please explain your answers.
a. Host A is sending Host B a large file over a TCP connection. Assume Host B has no data to send Host A. Host B will not send acknowledgements to Host A because Host B cannot piggyback the acknowledgements on data.
b. The size of the TCP RcvWindow never changes throughout the duration of the connection.
c. Suppose Host A is sending Host B a large file over a TCP connection. The number of unacknowledged bytes that A sends to B cannot exceed the size of the receive buffer in Host B.
d. Suppose Host A is sending a large file to Host B over a TCP connection. If the sequence number for a segment of this connection is m, then the sequence number for the subsequent segment must be m+1.
e. The TCP segment has a field in its header for RcvWindow.
5. Suppose Host A sends two TCP segments back to back to Host B over a TCP connection. The first segment has sequence number 526; the second has sequence number 1526.
a. How much data is in the first segment?
b. Suppose that the first segment is lost but the second segment arrives at B. In the acknowledgement that Host B sends back to Host A, what will be the acknowledgement number?
6. UDP and TCP use 1s complement for their checksums. Suppose you have the following three 8-bit bytes: 01011111, 01110000, 11001001. What is the 1s complement of the sum of these 8-bit bytes? (Note that although UDP and TCP use 16-bit words in computing the checksum, for this problem you are being asked to consider 8-bit sums.) Show all work. Why is it that UDP takes the 1s complement of the sum; that is. Why not just use the sum? With the 1s complement schema, how does the receiver detect errors? Is it possible that a 1-bit error will go undetected? How about 2-bit error?
7. Consider the following plot of TCP window size as a function of time. Assume TCP Reno is the protocol experiencing the behavior shown above, answer the following questions. In all cases, you should provide a short discussion justifying your answer.
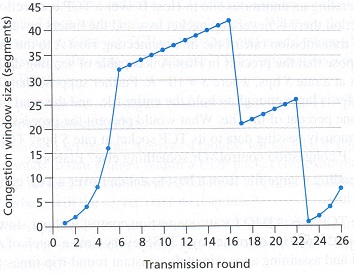
a. Is TCP Congestion avoidance operating in interval [6, 16]? Why or why not?
b. Is TCP congestion avoidance operating in interval [23, 26]? Why or why not?
c. After the 16th transmission round, is segment loss detected by a triple duplicate ACK or by a timeout? Why?
d. After the 22nd transmission round, is segment loss detected by a triple duplicate ACK or by a timeout? Why?
e. What is the value of Threshold at the 25th transmission round?
f. What is the value of Threshold at the 6th transmission round?
8. Socket Programming Assignment: Web Server (page 179)
In this lab, you will learn the basics of socket programming for TCP connections in Python: how to create a socket, bind it to a specific address and port, as well as send and receive a HTTP packet. You will also learn some basics of HTTP header format.
You will develop a web server that handles one HTTP request at a time. Your web server should accept and parse the HTTP request, get the requested file from the server's file system, create an HTTP response message consisting of the requested file preceded by header lines, and then send the response directly to the client. If the requested file is not present in the server, the server should send an HTTP "404 Not Found" message back to the client.
Code
Below you will find the skeleton code for the Web server. You are to complete the skeleton code. The places where you need to fill in code are marked with #Fill in start and #Fill in end. Each place may require one or more lines of code.
Running the Server
Put an HTML file (e.g., HelloWorld.html) in the same directory that the server is in. Run the server program. Determine the IP address of the host that is running the server (e.g., 128.238.251.26). From another host or the same host if you run the server on the local manchine, open a browser and provide the corresponding URL.
‘HelloWorld.html' is the name of the file you placed in the server directory. Note also the use of the port number after the colon. You need to replace this port number with whatever port you have used in the server code. In the above example, we have used the port number 6789. The browser should then display the contents of HelloWorld.html. If you omit ":6789", the browser will assume port 80 and you will get the web page from the server only if your server is listening at port 80.
You can also run the server program on your own PC and access the webserver from the same PC using the IP address for local host (127.0.0.1).
Then try to get a file that is not present at the server. You should get a "404 Not Found" message.
What to Hand in
You will hand in the complete server code along with the screen shots of your client browser, verifying that you actually receive the contents of the HTML file from the server.
Skeleton Python Code for the Web Server (Use the code on the next page as the skeleton of your .py file and insert lines of code needed between #Fill in state and #Fill in end. Please note that Python programs get structured through indentation, copy and paste may change the indentation of the following lines. You are suggested to use Python 3.x.
#import socket module
import socket
import sys
serversocket = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
print("Socket Created!!")
try:
#bind the socket
#fill in start
#fill in end
except socket.error as msg:
print("Bind failed. Error Code: " + str(msg[0]) + "Message: " + msg[1])
sys.exit()
print("Socket bind complete")
#start listening on the socket
#fill in start
#fill in end
print('Socket now listening')
while True:
#Establish the connection
connectionSocket, addr = #fill in start #fill in end
print('source address:' + str(addr))
try:
#Receive message from the socket
message = #fill in start #fill in end
print('message = ' + str(message))
#obtian the file name carried by the HTTP request message
filename = message.split()[1]
print('filename = ' + str(filename))
f = open(filename[1:], 'rb')
outputdata = f.read()
#Send the HTTP response header line to the socket
#fill in start
#fill in end
#Send the content of the requested file to the client
connectionSocket.send(outputdata)
#close the connectionSocket
#fill in start
#fill in end
print("Connection closed!")
except IOError:
#Send response message for file not found
#fill in start
#fill in end
#Close the client socket
#fill in start
#fill in end
serverSocket.close().