Network Design Exercise
Design Project -
Objective - The task is to develop a network for a multi site company.
This exercise attempts to give experience of a real world design that you may be asked to do in your future employment. As a result, only minimal guidance is given. You will need to fall back on all the experience that you have gained from the previous exercises. You will be assessed based on the decisions you made in each stage of the project.
Overview
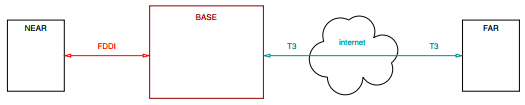
The network to be designed connects computers across three sites. The main site, called "Base" has four floors connected via a fast backbone network. One external site is connected using FDDI, and the other uses a T3 link through the Internet (protected with a firewall).
The network should be analyzed and improvements recommended. An option to relocate some of the servers can be considered. The backbone network upgrade from serial to partially meshed should also be evaluated.
Tasks -
- Requirements analysis - create a detailed design requirement specification
- Project Planning - evaluate required tasks, plan task execution sequence and estimate individual task duration.
- Applications and profiles modeling - identify scenarios needed to complete the project.
- create a hierarchical network in Riverbed Modeler
- simulate scenarios
- modify the network to validate potential improvements
- create a project report
Assessment -
This is an individual project. You will be assessed as follows:
- Initial network planning (show your work)
- network topology
- network address spaces planning
- applications modeling methods (show your work)
- profiles modeling
- simulation and results
- report
For a successful assessment:
- ensure all included screen clips are readable
- every image has a reason to be included, and a description (not just a name)
- include screen clips showing each application and profile configuration detail
- include the DES Log, and a description of warnings and errors listed
- include traffic plots for individual applications/profiles that show how accurate the model is.
Project Report Structure Suggestion -
Project Overview:
- What is this project about?
- What is the project goal?
- Why this project?
- What is achieved?
Design Decisions:
- Design specification
- Functional block diagram
- Design architecture
- Verification plan
Design Decisions:
- Design specification
what models are needed
what is the functionality
- Functional block diagram
identify blocks and data flow
explain each block functionality
- Design architecture
explain each block implementation plan
- Verification plan
how to prove the unit is operating correctly
Design Implementation:
- Explain each block implementation specifics
- Include schematics
- May include simulation data or diagrams
Design Issues:
- Highlight core issues
- What was easy to implement?
- What was difficult to implement?
- What works as planed?
- What does not work as planed?
- What is not implemented?
Test Report:
- Explain each test:
what functionality is addressed?
what is the pass/fail criteria?
what is the test result (pass or fail)?
include relevant diagrams.
Conclusion:
- Summary:
what was the project goal?
what is achieved?
what worked or did not work?
what could be done to improve the design functionality?
what could be done to improve the design implementation?
Attachment:- Assignment File.rar