Fundamentals of Computer Networks: Case Study
For this assignment you will be working in groups of five, however there is a part that will need to be completed individually.
Please note the team leader submits the group work AND their own section AND the packet tracer file. The remaining team members submit ONLY their 1000 word section.
Ensure that all of your work is word processed in a format which can be easily understood by someone without detailed network knowledge. In addition, ensure that all of your work is referenced where applicable. If you have any problems with referencing, then please do ask your tutor who can explain this, or help is available in the library.
When doing your team work, break the project into sections so that one person does not end up doing everything. If there are any issues with this then as the first instance talk to the person who you have decided will lead the project. If there are any issues though with this or it is the project lead where the problem is then do contact the module leader to discuss this.
Case Study Guidance & Deliverables
Scenario -
A new company specialising in hosting e-sports events, is facing issues in the design of a suitable network to support their business. They have decided to build a number of regional centres from where they can run e-sport events and host other events such as LAN parties. Their main centre which contains the server-class hardware is located in Manchester, this is from where they host events. They have planning permission to build four venues in Stockport, Birmingham, Liverpool and London.
They currently have no connections between these sites or a LAN design for them. The internal IP addresses are shown in Fig 1 below. No site has any design.
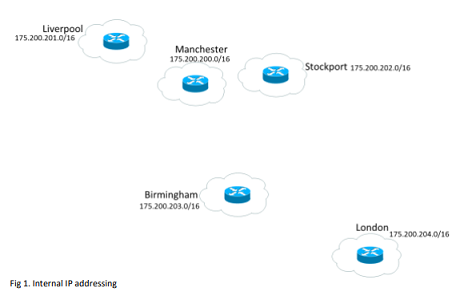
As this is a new venture you have been asked to design and implement both the internal and external networks. The company are keen to standardise their approach and have said that Liverpool, Stockport, Birmingham and London should be identical but use the IP addresses given in Fig 1. Manchester will need a separate design to incorporate the server class hardware as well as being able to host games.
Requirements Specification
Manchester will be its own ISP.
How you connect the sites using an appropriate WAN technology is your choice. You will need to assign an appropriate IP address to these WAN links.
Within each of the four sites (Liverpool, Stockport, Birmingham and London) you need:
- 20 admin machines
- 20 IP phones
- 300 wired machines for competitors to use, (split into 30 blocks of addresses, 10 machines per team)
- 40 IP Cameras for security
- 4 network printers
- 100 Fire precaution devices
- A DHCP server to issue addresses, each of the above specifications will need its own subnet
Address translation and ACL
Manchester needs a secure separate section to its network containing:
- 50 server class machines
- 10 admin/management machines
- 10 finance department machines
- 2 network printers
- 5 machines for the security team
Group section -
As a part of this assignment you will need to produce a report which discusses the following:
An IP addressing scheme for one of the sites (Liverpool, Stockport, Birmingham and London) the only difference being 1 digit in the third octet)
An IP addressing scheme for Manchester
Router/Switch configurations for that site demonstrating DHCP, NAT/PAT and an ACL (supplied as a functioning packet tracer file)
Standard configuration (passwords, naming etc.)
A discussion as to the benefits and requirements for VLANs within the network
Demonstrate the use of VLANS and MAC address security, with base configuration and management interfaces within your packet tracer file.
Generate an Access Control List which will meet the security requirements:
- Only allow the following ports to be used externally between sites: 22, 25, 80, 110, 443, 3000 - 3010
- Teams cannot directly access each other
- The security team only have access to the security equipment and ports 80 and 443
- Only the management team should have access to port 22
- All users can use the main printers
- At Manchester, only finance staff members can use the 2 separate network printers
Competitor machines should only be able to access the servers located in Manchester
Discuss the requirements for the WAN connections.
This is in terms of:
- Where to connect
- What throughput is needed
- What WAN technologies are available to connect the infrastructure with the benefits and risks
- Cost of this technology
- WAN link redundancy
This section of the report will be a maximum word count of 2000 words.
In addition to this section of your report you will need to give a group presentation on your work in a professional manner. This will be presented to the teaching team, not each other. In this presentation you are not expected to give every detail of what you have written but instead summarise the work for the benefit of the interested audience. You will also need to show a packet tracer implementation of your design during this presentation, you will be asked questions at the end of the presentation.
Need only calculations and packet tracer file and all the IP sub-netting as a word document.
Attachment:- Assignment File.rar