Assignment: Network Routing and Switching
PART A
Question 1
An organisation has been granted a block of addresses with the mask /24. If the organisation creates 8 equal-sized subnets, how many addresses (including the special addresses) are available in each subnet? Show your calculations.
Question 2
Give an example of a valid classful address that has a CIDR mask of /8.
Question 3
What does "path MTU discovery" in IPv6 refer to?
Question 4
What is the size of an IPv4 header with 10 bytes of options?
Question 5
Explain why IPv4 datagrams contain a checksum, but IPv6 datagrams do not.
Question 6
In a UDP packet, what is the difference between a well-known port number and an ephemeral port number apart from their numeric ranges?
Question 7
In your own words, briefly explain the function of the garbage collection timer in RIP.
Question 8
What is the difference in function between primary and secondary DNS servers?
Question 9
What is the purpose of an access point in a Wi-Fi network?
Question 10
Explain the default route entry in a routing table.
Question 11
A router processes a packet's destination address to determine the next hop. At what point in the process is ARP consulted and for what purpose?
Question 12
What is the purpose of the hop limit field in the base header of an IPv6 datagram?
Question 13
List three differences between UDP and TCP.
Question 14
What is the size of the base header in IPv6 expressed in bytes?
PART B
Question 1
An organisation has been allocated the following block of classless addresses by its ISP: 137.77.217.6/28
Identify the addresses in this range that would be used as the network address, those that can be used by network hosts, and the direct broadcast address.
Question 2
A company has been granted a block of addresses which starts at 200.100.20.0/23. Create the following 8 subnets for this company by calculating the subnet address for each subnet.
(a) 2 subnets with 64 addresses each
(b) 4 subnets with 32 addresses each
(c) 2 subnets with 16 addresses each
Question 3
IPv6 was predicted to replace IPv4 by 2010, however this has not happened. One reason for this delay was the introduction of classless addressing. Explain the reason that classless addressing led to the low adoption rates of IPv6.
Question 4
The figure below shows the configuration of a hypothetical section of the Internet.
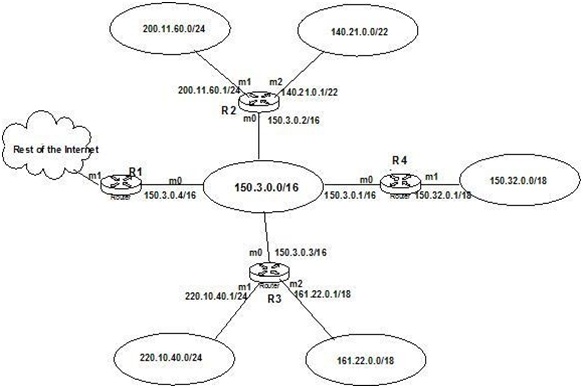
Construct the routing table of router R4 for this configuration by copying and completing the following table in the Examination Answer Booklet.
PART C
Question 1
Discuss how fixed-length classful addressing affects organisations in terms of address allocation, and how subnetting, supernetting, and Classless Inter-Domain Routing (CIDR) have helped resolve these issues.
Question 2
Briefly contrast the cost metrics between distance vector routing algorithms and link state routing algorithms for building routing tables, and briefly compare two major routing protocols that use them.
Question 3
The period between the phasing out of IPv4 and the general adoption of IPv6 is referred to as the "transition period". During this period, both IPv4 and IPv6 will need to be supported at the same time. Describe the main technical issues with having an Internet with mixed IPv4 and IPv6 routing, and the methods being developed or proposed to overcome these issues.
Question 4
Three types of wireless network architectures exist: the Independent Basic Service Set (IBSS); the Extended Service Set (ESS) and Mesh Wireless (MW) networks.
Briefly describe the essential differences between IBSS, ESS and MW and comment on where each architecture might appropriately be utilized.