Problem1:
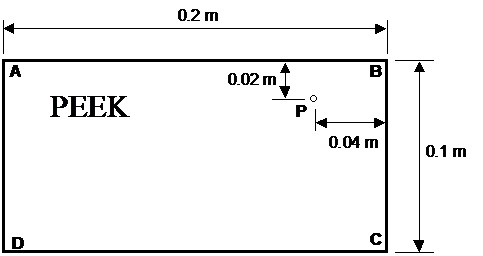
Make a computer code to simulate following solidification situation throughout a casting process:
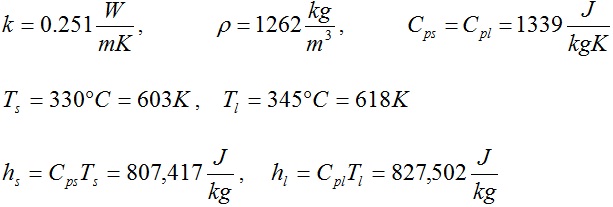
The material is a well-known polymer named as PEEK (polyetheretherketone). The properties of this material are as follows:
Suppose that Tinitial = 650 K everywhere (the pouring temperature) and that at time = 0 the wall temperatures on walls AB, BC, AD, and DC are set to Twall = 290 K (the mold temperature). Study this solidification problem numerically, and hand in following:
• A copy of your source code
• Plots of T centre versus time and Tp versus time
• The total solidification time and final point of solidification within the product.
• Contour plots of solidus and liquidus interfaces for a certain time.
• A plot showing the temporal progression of solidus interface fronts during the casting process.
Run your code several times with a deceasing mesh cell size. For each of these mesh cell sizes, report on the following:
• The total solidification time and final point of solidification within the product.
From this mesh size sensitivity analysis suggest an optimal mesh size to address this type of problem.
δ^2*T/δx^2
Δ/Δx * ΔT/Δx