problem 1)a) Describe priority queues.
b) prepare the program to implement priority queue using structures.
c) prepare functions to perform the postorder and preorder traversal of a binary tree.
problem 2)a) Sort the given set of numbers using merge sort showing clearly the different steps sorting.
60, 50, 25, 10, 35, 25, 75, 30.
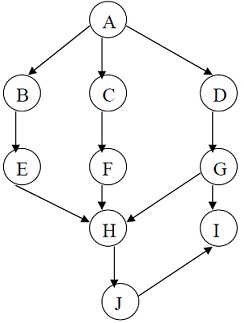
b) prepare the depth first traversal and breadth first traversal for the following graph starting from vertex A.
problem 7)a) Define Hashing and Hash collision.
b) Describe different techniques used to resolve hash collision.
c) Describe the array of adjacency list representation of an undirected graph with the ex.